Customer data security is no longer optional. In 2026, with over 20 U.S. state data privacy laws active alongside GDPR and evolving AI regulations, every company handling customer information faces real consequences for getting it wrong.
The average data breach now costs $4.88 million, according to IBM’s 2025 report. Beyond the financial hit, 82% of consumers say they avoid companies with poor data protection practices. For support teams managing tickets, chats, and sensitive files daily, the stakes are personal.
This article walks through 7 practical strategies any business can start applying this quarter. These are not abstract enterprise frameworks. They are concrete steps designed for startups and growing SaaS teams that need to protect customer data without slowing down operations.
Why Is Customer Data Security In 2026
The regulatory landscape has shifted dramatically. California’s CPRA now requires mandatory cybersecurity audits, and the EU AI Act classifies customer support AI as high-risk when processing sensitive data.
Meanwhile, threats have grown more sophisticated. GenAI-powered phishing and deepfakes rose 300% in 2025. Human error still causes 68% of breaches, and 52% of incidents trace back to third-party vendors.
Economic pressure mounts quickly after a breach. Mid-sized firms lose an average of $10 million in revenue, with 15-20% customer churn following public incidents. Protecting customer data is not just about regulatory compliance. It directly protects your business operations and bottom line.
Customer Data Security Framework: 7 Strategies Every Company Should Follow
These 7 strategies build on each other and form a layered defense for your customer data. You can roll them out over a 3-6 month roadmap, starting with quick wins that deliver immediate risk reduction.
The tone here is practical. Every recommendation draws from real SaaS and support team scenarios, with clear steps you can take this week.
1. Map, Classify, And Minimize The Customer Data You Hold
You cannot secure what you do not know exists. According to Gartner, companies overlook 30-50% of their data holdings. Your first step is creating a simple data map.
Audit your core tools: CRM fields in Salesforce or HubSpot, ticket data in your helpdesk, payment details in Stripe, and files in cloud storage like Google Drive. Document what customer information lives where, and make sure your team understands the benefits of using a modern ticketing system to keep this data organized and auditable.
Next, classify data by sensitivity:
| Classification | Examples | Support Context |
|---|---|---|
| Public | Marketing emails, blog comments | Published FAQs |
| Internal | Ticket summaries, agent notes | Team dashboards |
| Confidential | Customer addresses, support history | Most ticket content |
| Highly Sensitive | SSN, full card numbers, health notes | Billing disputes, compliance tickets |
Apply data minimization by reviewing each form and ticket field. Do you need the date of birth after account verification? Can you truncate credit card numbers to the last 4 digits? Remove fields that serve no ongoing purpose.
Set specific data retention periods. Delete closed tickets with low-risk data after 18-24 months. Redact payment snippets within 30-90 days. Document this in a one-page internal policy to support regulatory compliance.
2. Lock Down Access With Least Privilege And Strong Authentication
Least privilege means giving users only the data access they need for their specific role. A new support agent should see only tickets for their team and region. Finance data stays visible only to finance roles.
Start by enabling role based access control in your helpdesk and CRM. Remove shared logins from support inboxes immediately. Run a monthly review of admin rights across your tools. Adopting the best ticket management system for your team can make these access controls easier to configure and maintain. Research shows the average company has 10 times more over-privileged accounts than necessary, creating serious insider threats.
Implementing multi factor authentication is essential for every account touching customer data. MFA blocks 99.9% of phishing attacks according to Microsoft research. Use authenticator apps like Google Authenticator for standard users and FIDO2 hardware keys for admins handling sensitive files.
Handle offboarding on the same day someone leaves. Use a simple checklist covering email, helpdesk, cloud drives, and analytics tools. The 2022 Uber breach exploited ex-employee access that lingered for 7 months, exposing how poor access management creates unnecessary risk.
3. Encrypt Data In Transit And At Rest
Data at rest means information stored on disks, like your ticket database. Data in transit means information moving between systems, like chat messages syncing to your CRM.
Both need protection. For transit, enforce TLS 1.3 and HTTPS across all customer-facing pages and APIs. For stored data, use AES-256 encryption where supported, which is the NIST-approved standard used by AWS and other major cloud environments.
Verify your vendors handle data encryption properly. Add scored questions to your vendor security questionnaires: “Does your platform encrypt data at rest with AES-256?” and “Do you support customer-managed encryption keys?” For cloud tools, also confirm they meet your criteria for the right cloud helpdesk solution for your team.
Secure your backup files too. Ensure backups are encrypted, stored in at least two regions, and tested quarterly to confirm they can restore real customer tickets. About 20% of organizations discover their backups were unencrypted only after needing them during an incident.
4. Build Secure Processes Around Your Support Tools
Customer data leaks often start in daily support operations. Screenshots with visible PII, file attachments containing malware, internal notes with unmasked SSNs, and escalations that copy sensitive information into insecure channels.
Create simple written guardrails for agents, and back them up with efficient support ticket management using EasyDesk:
- Never paste full card numbers into tickets, use payment tokens instead
- Mask national ID numbers (show only last 4 digits)
- Never put passwords into chat logs or ticket notes
- Share billing information through secure portal links, not email attachments
Here is a concrete example: when handling a billing dispute, share a redacted invoice link via your secure customer portal. Do not email the full credit card details or attach the original invoice with all payment data visible.
Support managers should review a 5% sample of tickets each month for policy violations. Use these as coaching moments to protect sensitive information rather than blame sessions. Tools like auto-redaction can catch mistakes before they become data exposure incidents, especially when combined with modern ticketing software and support best practices.
5. Train People So They Stop Being The Easiest Way In
Human error causes 74% of breaches according to Verizon’s 2025 DBIR. Phishing succeeds against 36% of untrained staff but only 3% of trained employees. The MGM 2023 ransomware attack started when a social engineering call tricked a single support agent.
A lightweight security awareness program works for teams of 10-50 people. Run quarterly 30-minute sessions using short videos from platforms like KnowBe4. Include realistic phishing simulations that show improvement over time.
Train employees to develop these key behaviors:
- Verify sender authenticity before clicking links (check SPF/DKIM)
- Confirm customer identity through callback before sharing account information
- Use password managers for all work accounts
- Report suspicious emails instead of ignoring or deleting them
Assign role-based training. Admins and team leads who handle exports and integrations need deeper sessions on data security practices. Occasional tool users need lighter training focused on basics like phishing recognition.
6. Monitor, Log, And Respond To Incidents Fast
Without visibility into who accessed what and when, you cannot investigate effectively after something goes wrong. IBM research shows 52% of breaches go undetected for over 200 days, giving attackers extended access to customer information.
Turn on audit logs in your core systems: helpdesk, CRM, and identity provider. Retain access logs for 12-24 months to satisfy data protection regulations like CCPA and support forensic investigations, and make sure your tools, such as helpdesk ticketing software, expose those logs in a way your team can actually use.
Create a lightweight incident response plan. This should be a 1-2 page document covering:
| Element | Details |
|---|---|
| Roles | Incident commander, technical lead, communications owner |
| Decision authority | Who determines whether to notify customers |
| Notification thresholds | GDPR requires 72-hour authority notification |
| Communication channels | Email, Slack, phone tree |
7. Stay Compliant With Key Privacy And Security Regulations
Security protects data. Privacy governs how you collect, use, and retain it. Both matter for protecting customer data.
Major frameworks relevant to customer support:
- GDPR: Applies to EU user data. Fines up to 4% of annual revenue or €20M. Requires responding to data subject rights requests within 30 days.
- CCPA/CPRA: Covers California residents. Requires opt-out options for data sales and mandatory audits starting 2026.
- PCI DSS: Applies to cardholder data. Requires quarterly security scans and strict data retention limits.
For smaller teams, build a simple compliance roadmap: map your data flows using tools like Lucidchart, publish a clear privacy policy at /privacy, set up consent management platforms for preferences, and document your security controls for audits.
Customers increasingly request security reviews when buying SaaS products. Having a basic security and privacy summary ready can shorten sales cycles by 20% and build customer trust before contracts are signed.
Common Customer Data Security Risks Facing Support Teams
Customer support tools are attractive targets because they centralize emails, chats, and files from thousands of accounts. Understanding how a help desk improves support behind the scenes also highlights how much risk concentrates in one place. A 2025 SaaS Security Survey found that 28% of SaaS breaches specifically targeted helpdesk environments.
Several concrete risk patterns affect support teams daily. Shared passwords on support inboxes let one compromised credential unlock access to years of customer conversations, whereas a well-managed shared inbox for customer support teams can enforce clear ownership and accountability. Misconfigured cloud storage for attachments can expose sensitive files to anyone with the right URL. Public status pages sometimes leak ticket IDs or customer references that attackers use for social engineering.
One 2024 incident involved a SaaS company that misrouted an email thread, exposing 5,000 customer names and emails to the wrong support queue. This traced directly back to missing access controls and unclear processes around ticket routing.
Each of these risks connects to the strategies above. Mapping data prevents surprises (Strategy 1). Strong access control blocks credential misuse (Strategy 2). Secure processes catch routing errors before they become data breaches (Strategy 4).
How To Implement These 7 Strategies Without Slowing Your Team Down
A 90-day rollout makes these strategies achievable without overwhelming your team or business operations, especially when you align them with the right helpdesk setup for your support team.
Month 1: Foundation
- Complete your data map across CRM, helpdesk, and cloud storage
- Enable role based access control in core tools and invest in smarter helpdesk setups for smoother support
- Remove shared logins and begin MFA rollout
Month 2: Protection
- Finish implementing multi factor authentication for all accounts
- Document and distribute security policies to agents, and pair them with ticket automation that streamlines customer support
- Run your first phishing simulation and training session
Month 3: Visibility
- Enable audit logging in helpdesk and identity systems while moving toward a smarter cloud-based help desk platform
- Create your incident response plan
- Complete vendor security reviews for top 5 integrations
Get buy-in from founders by mapping each security step to business risk. A breach can cost 1-3 months of revenue. Frame security controls as revenue protection, not IT overhead.
Implementation works best when iterative. You do not need a perfect zero-trust architecture on day one. Improve one concrete control each sprint and build momentum.
Common Customer Data Security Mistakes Companies Make
Companies often invest in technology, yet still overlook critical practices that support strong customer data protection. Security failures usually happen when teams treat security as a one-time technical setup instead of a continuous responsibility. Following proper security principles helps organizations protect customer information, reduce risks of identity theft, and avoid regulatory penalties. When companies ignore these key principles, they expose themselves to data misuse, non-compliance with regulations, and potential hefty fines.
Weak Password Policies
Weak password policies remain one of the most common mistakes in customer data protection. Simple passwords or shared login credentials make it easier for attackers to gain access to sensitive accounts. When organizations fail to protect sensitive data with strong authentication practices, unauthorized users may access customer records or internal systems, even if they use a powerful ticketing software platform for customer support.
Modern security software supports stronger identity protection through measures such as multi factor authentication and strict password enforcement. These best practices ensure that only authorized individuals can access sensitive systems and customer data. Without these safeguards, attackers may exploit compromised credentials and cause significant damage through identity theft or financial fraud.
Unsecured Third Party Integrations
Third party integrations are useful for connecting software tools, but they also introduce risks if not reviewed carefully. Many companies connect external services without evaluating how those services handle consumer data protection. Weak integration security can expose behavioral data, stored customer information, or internal databases to unauthorized systems.
Organizations must verify how partners store, process, and secure sensitive data before allowing system connections. Proper integration reviews should confirm encryption standards, data handling practices, and data protection compliance. Following these best practices ensures companies protect customer information and maintain responsible data privacy management.
Lack Of Employee Security Training
Employees play a critical role in securing data across business operations. Without proper training, staff may accidentally expose sensitive files or fall victim to phishing attacks. Human errors often lead to data misuse or accidental exposure of confidential customer data.
Organizations should train employees regularly on securing data, identifying suspicious emails, and following security procedures. Security training also helps employees understand how to handle behavioral data and other forms of sensitive information responsibly. When companies educate their teams, they strengthen consumer data protection and reduce the risk of security incidents.
Poor Access Management
Improper access management creates opportunities for unauthorized users to gain access to internal systems. When organizations fail to control access or remove permissions from former employees, sensitive information remains exposed.
Limiting access to only authorized individuals is a fundamental step in protecting customer data. Companies should implement role based access controls and review access permissions regularly, ideally within a ticketing software built for better customer support that makes permissions easy to manage. These security measures help organizations secure sensitive data while preventing internal threats.
Inadequate Data Backup Policies
Backup systems are essential for protecting organizations from ransomware attacks or accidental data loss. However, some companies neglect proper backup strategies, leaving stored data vulnerable. If attackers compromise backup files, organizations may lose critical business information permanently.
Effective backup policies support customer data protection by storing encrypted copies of data across multiple locations. These policies help companies recover quickly after cyber incidents while maintaining regulatory compliance. Strong backup strategies remain one of the most important best practices for securing data and ensuring long term business stability, and your choice between cloud-based vs on-premise helpdesk deployments will influence how you design those backups.
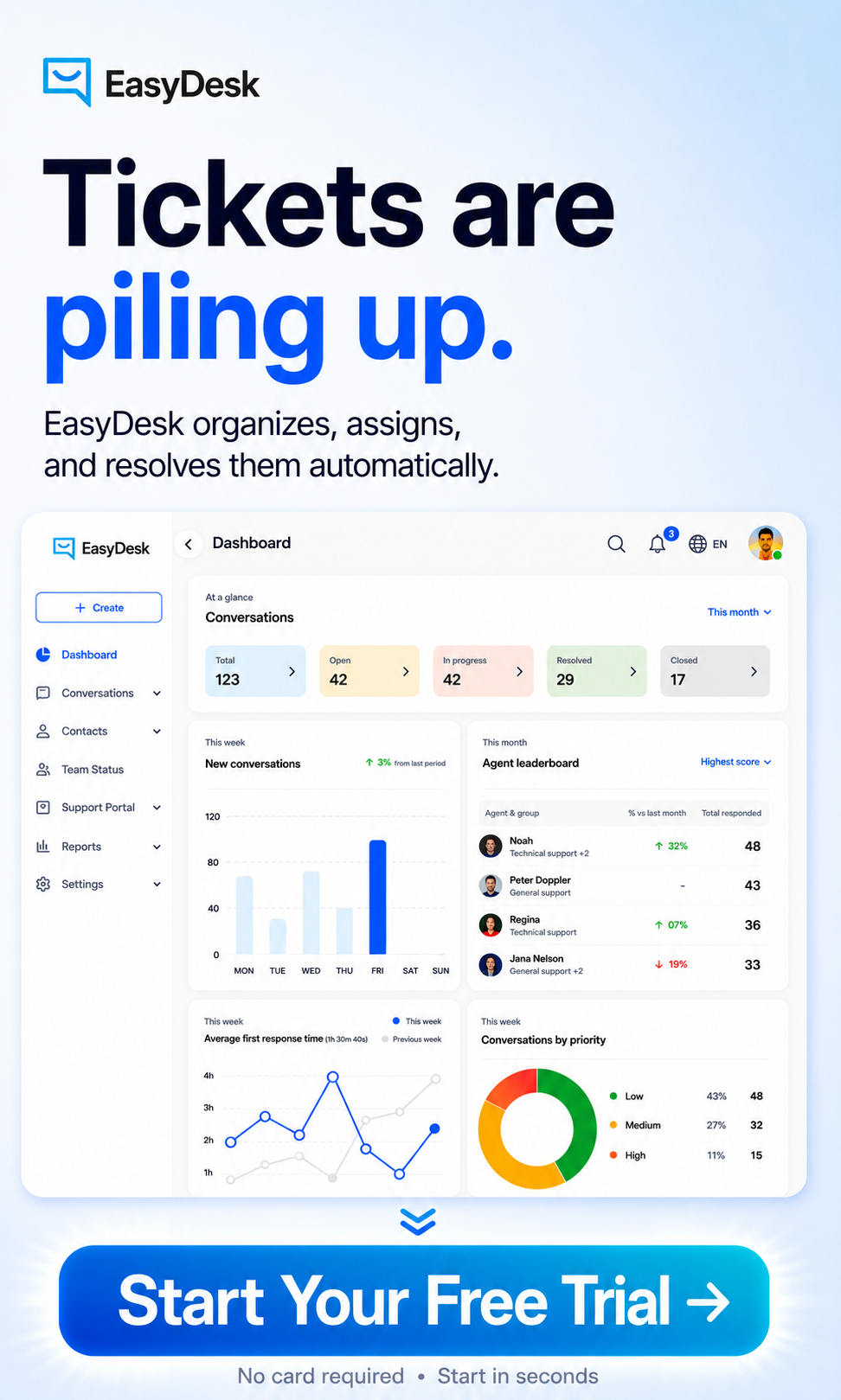
How does EasyDesk Helps Protect Customer Data security?
EasyDesk embeds security directly into its helpdesk platform, so teams gain access to protection without complex configuration or separate tools.
Granular role based access control prevents over-privileging by limiting what each agent can view and edit. Automatic data encryption protects tickets both in transit and at rest, meeting standards for data confidentiality without manual setup.
Audit logs track all ticket changes and agent actions, supporting both incident response and maintaining compliance with data protection laws. IP whitelisting and native MFA block unauthorized access attempts before they reach customer information.
Secure chat and attachment handling avoid the leaks that occur when teams use side channels. Configurable data retention settings help minimize data collection and support timely data deletion when records are no longer needed.
For startups scaling their support operations, EasyDesk simplifies compliance while delivering the security controls that larger organizations require. The platform supports compliance efforts for GDPR, CCPA, and other data privacy management requirements without forcing teams to build everything from scratch.
FAQs
How Much Customer Data Is Too Much For A Small Company To Store?
There is no fixed number. GDPR and CCPA both say you should store only the data necessary to serve customers effectively. Review each field you collect and ask whether you need full addresses or just city and state, whether date-of-birth serves any purpose after verification, and whether you can truncate identifiers. Audit your signup forms and integrations quarterly to identify unnecessary data usage and reduce your exposure.
Do We Need A Dedicated Security Team To Protect Customer Data?
Most startups and small businesses do not begin with a full security team. However, someone should own security responsibility, even if it is a small committee or a single person with allocated time. Use managed services and secure SaaS tools like EasyDesk features for secure customer support that handle encryption, logging, and access management by default. Revisit this decision when you pass 50 employees, enter regulated markets, or handle payment data directly.
What Should We Do In The First 24 Hours After A Suspected Data Breach?
Stay calm and follow a clear process. First, contain the incident by freezing affected accounts without deleting evidence. Preserve all logs and notify your executive team and technical lead. Check whether GDPR’s 72-hour notification requirement or other data protection regulations apply. Communicate with affected customers honestly, even before you have complete details. Transparency preserves more customer trust than silence or vague statements about ongoing investigations.
How Can We Prove To Customers That We Take Data Security Seriously?
Publish a concise security overview on your website explaining your encryption practices, access controls, and data retention policies in plain language. Offer security-conscious customers additional details like vendor lists, SOC 2 summaries, or transparent customer support pricing and plans when requested. Consistent behavior matters most: visible MFA use, quick vulnerability fixes, regular updates, and secure defaults in tools like EasyDesk demonstrate commitment beyond marketing claims.
What Role Does Our Helpdesk Platform Play In Overall Customer Data Security?
Your helpdesk is often the main hub for sensitive personal information, making its security posture critical to overall risk. A modern helpdesk should offer strong authentication options, granular roles and permissions, secure APIs, and reliable action logging. Choosing a platform like the EasyDesk customer support platform with these controls built in makes it easier for smaller teams to meet customer expectations and regulatory requirements without custom development.